Viscosity 1.10.6 (1790) Crack + Keygen Download
The Internet is full of dangers just waiting for the right moment to strike weak or unsecured connections. Nowadays, with businesses being dependent of the web, you need to make sure that no one can trace your actions, to decrease the risk of being the victim of a virtual attack. Applications such as Viscosity offer a helping hand in this regard, allowing you to create a secure tunnel through which to safely access every part of the internet.
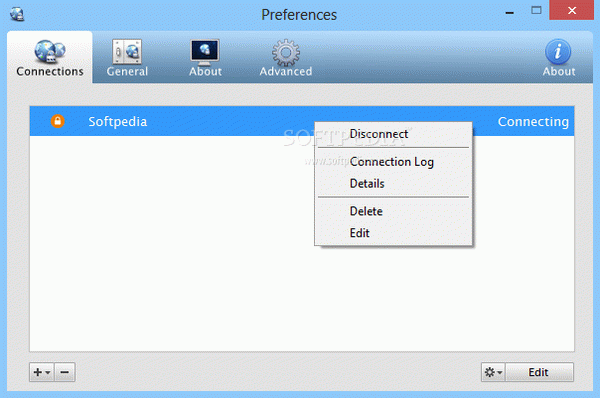
First off, you need to set up at least one connection before being on the safe side. This is easily done from the preferences window and you are not limited to a single one. However, if you already have a configuration file saved on your computer it can be used as such. The same applies for a server, with the possibility to import connection data once your credentials are provided.
Download Viscosity Crack
| Software developer |
SparkLabs
|
| Grade |
4.4
1137
4.4
|
| Downloads count | 9986 |
| File size | < 1 MB |
| Systems | Windows Vista, Windows Vista 64 bit, Windows 7, Windows 7 64 bit, Windows 8, Windows 8 64 bit, Windows 2003, Windows 2008, Windows 2008 64 bit, Windows 2008 R2, Windows 10, Windows 10 64 bit |
If neither of the import methods provide aid, you might need to set up a connection manually. This is where it gets tricky, with various requirement fields asking for technical info. The application lets you set authentication, networking or proxy options. Several SSL / TLS clients can be used for authentication, and for enhanced security you can opt for a username and password check.
What's more, your data can be kept safe by tunneling all data through a VPN connection. However, you must specify a default gateway, DNS details, with the possibility to include shaper, fragment, tun MTU and inactive.
As mentioned above, the application does not limit you to a single connection. You are free to organize more entries in folder for a better view. By default, the application requires you to manually connect to a created service, but this can be solved by an option that automates the task.
All in all, Viscosity Serial can come in handy to a large variety of business and individuals, by creating a suitable means of data transfer, without exposing it to hacks and attacks. Most of your attention is required when setting up connection, with the rest being handled by the application. In case you constantly need to connect to your work computer from remote locations, this is a proper utility.
