Snort 2.9.19 Crack Plus Activation Code
Snort provides you with a high-performance, yet lightweight and flexible rule-based network intrusion detection and prevention system that can also be used as a packet sniffer and logger. With its advanced capabilities and reliability, it is the most deployed IDS / IPS software, widely used in network monitoring applications.
Combining database signatures with anomaly-based scanning, Snort is capable of detecting unwanted intrusions and features real-time analysis and alerts. In order to work properly, the application requires WinPcap, a tool that provides direct packet access, allowing it to read raw network data.
Download Snort Crack
| Software developer |
Cisco
|
| Grade |
3.8
1127
3.8
|
| Downloads count | 34201 |
| File size | < 1 MB |
| Systems | Windows All |
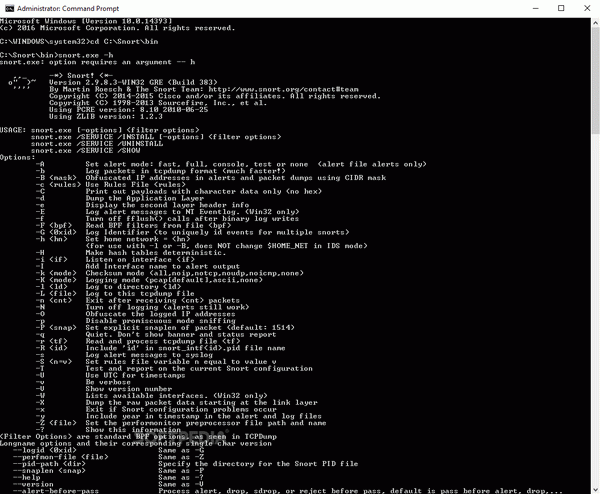
Having a Snort sensor up and running requires solid command line, network protocol functioning and IDS knowledge, thus beginner users might need to take their time to go through the documentation in order to learn how things work.
The application can be used as a packet sniffer and logger, monitoring the network traffic in real-time, displaying the TCP/IP packet headers and recording the packets to a logging directory or a database (MySQL, Oracle, Microsoft SQL Server, and ODBC are supported). However, the real power of Snort resides in its intrusion detection capabilities, since it can analyze network traffic and warn you about unusual events, vulnerabilities or exploits.
The user customizable rules are similar to a firewall application and define the behavior of Snort Serial in the IDS mode. You can set them up by editing the configuration file, which can also include application-specific rules (for SMTP e-mail connections, SSH and so on).
The program analyzes the sent and received packets and determines whether any of them represent a possible threat. The packets that trigger rules can be logged in ASCII or binary format, the latter being recommended for keeping up with a fast LAN.
Snort benefits from large community support with significant contribution to the rule database, which guarantees its reliability. Whether you use it for real-time traffic analysis and logging or as an IDS / IPS appliance, it is a powerful network security tool that professional users are surely to appreciate.
