Malwarebytes Breach Remediation 2.7.1.1627 Beta Crack With Activator
Security teams struggle to keep endpoints in a company free of malware, fighting threats and attacks on all fronts. Data security is vital in the business environment, so a thorough protection and threat detection system is a must in any organization.
Relying on an award-winning scanning engine, Malwarebytes Breach Remediation addresses security breaches with a whole new approach, promising to provide small to large companies a fast way of detecting malware on multiple endpoints and removing suspicious or dangerous files without leaving exploitable traces behind.
Download Malwarebytes Breach Remediation Crack
| Software developer |
Malwarebytes
|
| Grade |
4.1
819
4.1
|
| Downloads count | 6055 |
| File size | < 1 MB |
| Systems | Windows XP, Windows Vista, Windows Vista 64 bit, Windows 7, Windows 7 64 bit, Windows 8, Windows 8 64 bit, Windows 2003, Windows 2008, Windows 2008 64 bit, Windows 2008 R2, Windows Server 2012, Windows 10, Windows 10 64 bit |
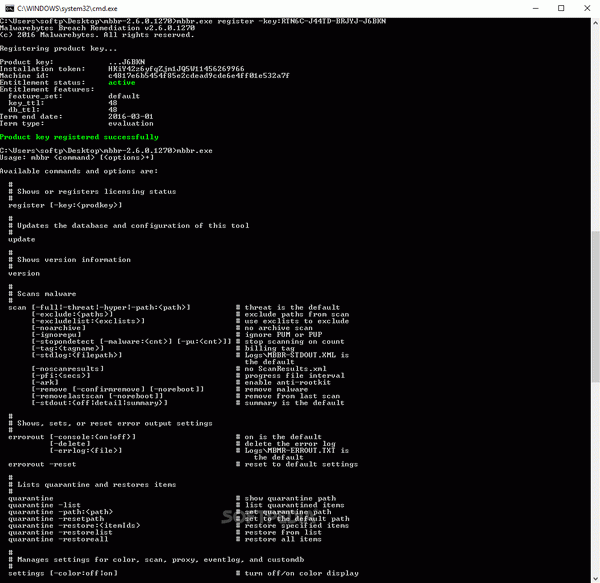
Categorized as an endpoint detection and remediation solution, Malwarebytes Breach Remediation only runs in the command prompt, but its syntax and its options are fairly simple. Before proceeding to start a new system scan, users must update the virus database to make sure the latest definitions are used.
The application is configured to analyze the entire system and network endpoints to detect suspicious files that might betray breaches and infections. Its progress can be monitored as the scan runs, and a brief statistics about the findings is displayed at the end. Aiming to treat the cause rather than apply temporary fixes, Malwarebytes Breach Remediation tracks and removes all the threat traces, cleaning compromised workstations, preventing future attacks, and thus laying the first brick for a stronger security system.
The array of behavioral and heuristics detection rules that the scanning engine includes can be enriched by loading custom rule files (in XML format) called custom indicators of compromise (IOC). There is a list of supported sources that includes other breach detection solutions, such as Fidelis, Lastline or Mandiant.
Full, thorough scans can be performed, but the user is allowed to specify the locations to exclude from the scan or the paths to analyze. Furthermore, archives, PUPs, and PUMs can be ignored, if the user wishes so. Malwarebytes Breach Remediation Serial also features an anti-rootkit module that must be enabled manually.
Files and components that are considered potentially dangerous are sent to quarantine, unless. Users can explore the quarantined items and restore any file with ease.
The purpose of Malwarebytes Breach Remediation is to implement a proactive security solution for all enterprises, which will reduce the time needed to address malware-related problems and allow teams to focus on more important company projects.
It can be launched without causing incompatibilities with the permanent security system, more so that the latter is a Malwarebytes product. Furthermore, it ensures seamless integration with known endpoint management systems, allowing quick and convenient deployment.
