MOBILedit Forensic Express 7.4.1.21502 Crack With Serial Key Latest
In today's world, almost no one walks around without a mobile phone, which became more of a necessity rather than a luxury. Aside from their contact list, people store all kinds of data on their phone, such as emails, documents, or media files, which transforms this personal handset into a resourceful collection of data that can offer clues about the phone owner. Thanks to the MOBILedit Forensic Express edition, investigators can extract the information they need from a phone and recover deleted data.
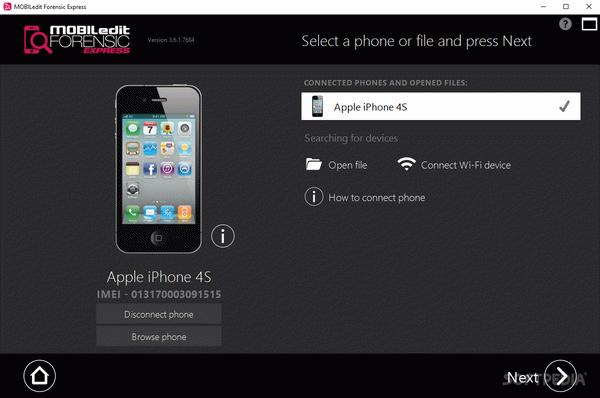
With a visually-appealing interface that works as a wizard, MOBILedit Forensic Express can provide step-by-step assistance in connecting to a phone and accessing its content.
Download MOBILedit Forensic Express Crack
| Software developer |
COMPELSON Laboratories
|
| Grade |
2.7
811
2.7
|
| Downloads count | 6265 |
| File size | < 1 MB |
| Systems | Windows 7 64 bit, Windows 8 64 bit, Windows 10 64 bit |
There is no need for you to go through a complicated configuration process, as MOBILedit Forensic Express automatically detects the phone as soon as it is connected to the PC. However, you do have to authorize the access of MOBILedit Forensic Express to the target handset. Please note that specific drivers might be required in order for the PC to recognize the phone.
Once the connection is set up, MOBILedit Forensic Express Serial makes it possible for you to explore its content. You use the so-called 'Source Viewer' to do so, which displays a double-sided commander to show both the phone's folder and a location on your computer.
You can use this file explorer to see the files stored on the phone and easily copy them to the target destination on your computer. MOBILedit Forensic Express can download a file from the phone and preview it, then copy it to a location of your choice. Multiple concurrent operations of this type are permitted.
The purpose of MOBILedit Forensic Express is to help its users extract data from a phone, analyze it and create a report to describe their findings. It can reveal installed apps on the target phone, and can be used to retrieve data that has been deleted. This helps investigators in finding potential evidence for their case inside a suspect's phone.
